Web Apps Overview
The SP360 Web Apps Dashboard offers significant functionality for continuous monitoring of Web App vulnerabilities. It enables you to get deep insights into different Key Performance Indicators (KPIs) for your Web Apps by offering many filters to configure your view into your vulnerability data. The Web App dashboard displays data through various charts that can be filtered and tailored as detailed in this help section.
This dashboard enables you to focus on the vulnerabilities that are most important for your organization. In addition to illustrating the “current state” of vulnerabilities, it also provides significant insight into the historical “trending” so you can see the progress your organization is making addressing any and all outstanding vulnerabilities.
Filtering Chart Content
For ease of use, the dashboard has options/buttons at the top of the dashboard that can be used to filter the chart information. In addition, the last section of the dashboard (i.e., the Web Apps list) allows you to include or exclude the Web Apps that contribute to the vulnerability data.
| Options/Buttons | Descriptions |
|---|---|
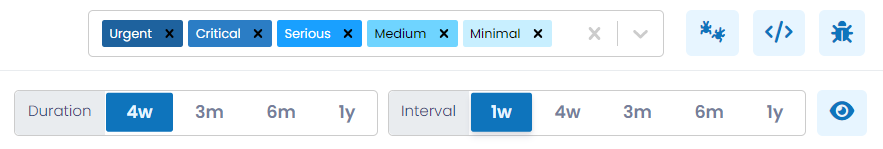
| Severity | From this drop-down you can select one or more severities of interest to alter the charts accordingly. The severity of each vulnerability is classified as either Urgent, Critical, Serious, Medium, or Minimal. |
| Duration | Using this control, you can establish the time-period the chart covers. The available options are 4 weeks, 3 months, 6 months or 1 year. |
| Interval | Using this control, you can establish the period of time each data point represents. The available intervals are 1 week, 4 weeks, 3 months, 6 months or 1 year. This option allows you to view the trending over the desired time periods; for example, month-over-month, or quarter-over-quarter. |
| Use this toggle button to view the vulnerability counts for each interval in all the charts. This removes the need to hover over the chart. | |
The Web Apps dashboard provides information in three sections:
- Vulnerabilities Trending History
- Current Vulnerabilities (i.e., current counts)
- Vulnerability Metrics
Vulnerabilities Trending History
The Vulnerability Trending History (which is a collapsible section) provides you with an overall trending of vulnerability counts, so that you can observe the progress made over time. The data is represented in charts (as shown above) and segmented with a separate chart for:
- Total Number of Vulnerabilities
- New Vulnerabilities
- Reopened Vulnerabilities
- Fixed Vulnerabilities
- Ignored Vulnerabilities
Note: In the lower four Trending Charts, you will find two annotations. The annotation displayed on top shows the number of vulnerabilities (i.e., New, Reopened, Fixed or Ignored) discovered since the completion of the last Interval chosen, so it represents a partial Interval. It grows by a day, each day.
The annotation displayed on the bottom shows the vulnerabilities discovered during the last full Interval retroactively from today, such as 1-week, 4-weeks, and so on. This is a moving interval that changes each day. When selecting a 1-week Interval, both annotations are “drillable”, allowing you to see the corresponding vulnerabilities. For Intervals other than 1-week, only the second annotation is “drillable”.
Total Number of Vulnerabilities
This chart shows the trending of all existing vulnerabilities (i.e., New, Reopened or Existing) and is filtered according to the controls discussed above. Often organizations will be most interested in the highest severity vulnerabilities and will limit the charts to Urgent and Critical vulnerabilities.
New Vulnerabilities
This chart provides you with insight into “new” vulnerabilities, meaning those vulnerabilities that were discovered for the first time within the chosen interval. For example, if you chose an interval of one week, the chart will show how many new vulnerabilities were found for each complete week, for the entire chosen duration.
Reopened Vulnerabilities
This chart provides you with insight into “reopened” vulnerabilities, meaning those vulnerabilities that were previously remediated, but re-discovered within the chosen interval. In general, “reopened” vulnerabilities should be rare.
Fixed Vulnerabilities
This chart provides you with insight into those vulnerabilities that have been remediated within the chosen interval. Most organizations find this insightful and will correlate these numbers to their most recent development or IT efforts.
Ignored Vulnerabilities
This chart provides you with insight about the “ignored” vulnerabilities for the chosen interval. Vulnerabilities may be manually ignored by users, or the application may “auto-ignore” any vulnerability that is associated with a Web App that was not reachable (scannable) in the past 30 days. You may choose to ignore a vulnerability if it is associated with an application that you know is about to be taken out of service, and therefore you do not want to clutter the dashboard with vulnerabilities that do not need to be explicitly addressed.
Current Vulnerabilities
Current Vulnerabilities (which is a collapsible section) provides you with charts that show the current vulnerability counts in the following categories:
- By Severity – allows you to quickly focus on the most severe vulnerabilities.
- By Status – to easily discern the current vulnerabilities statuses.
- Groups by QID – a grouping chart that shows your vulnerabilities in groups, to easily understand the types of vulnerabilities that are most common and that by addressing their underlying root cause can, enable you to address multiple vulnerabilities at a time.
By default, these counts are represented as bar charts. If you prefer to see the counts expressed as percentages and in a pie chart format, click the action icon to the right of the Current Vulnerabilities heading, as shown below.
The grouping chart, Top 10 Groups by QID provides a powerful additional functionality.
By clicking the action icon in the upper-right corner of that chart, you can view a pop-up (shown below) that lists all groups (not just the Top 10) and provides additional information, as well as the ability to apply bulk functions, such as ignoring all the vulnerabilities in that group. The action icon
allows you to see each vulnerability in the group, whereas
allows multiple vulnerabilities (with the same QID) to be ignored more conveniently with a single request.
Vulnerability Metrics – Severity
Vulnerability Metrics (which is a collapsible section and is collapsed by default) provides insights into how long your open vulnerabilities have been open, and how long it took to close your remediated vulnerabilities. Often organizations have Service Level Agreements (SLAs) that commit them to addressing vulnerabilities within a given timeframe, this information helps you understand how well you are adhering to your SLAs.
The Vulnerability Metrics are presented in one of two formats, that can be toggled by clicking the action icon on the upper-right hand portion of this section. By default, the Severity-based format is shown, which contains the following two bar charts.
Days (Average Time Open)
This bar chart shows the total number of open vulnerabilities (upper right notation) and the average number of days (upper left notation) that each severity of vulnerabilities has been open. Hovering over the chart will also show how many vulnerabilities were considered for the metric calculations.
Days (Average Time to Closure)
This bar chart shows the number of vulnerabilities closed in the specified time frame (upper right notation) and the average number of days (upper left notation) the vulnerability was open before being closed.
Clicking on the action icon to the far right of the Vulnerability Metrics, the header displays a “Timeband” label, and breaks down the number of vulnerabilities by ranges of days, for example, those open less than three days, or between three and seven days. This data is presented in pie chart format.
Notice that the icon used to toggle between Severity-based and Timeband-based formats changes.
Web Apps List
This sub-section of the dashboard allows you to tailor the vulnerability metrics being shown by including or excluding specific Web Apps. To better understand the operational details, let’s breakdown the key features this sub-section offers.
The upper left corner of the Web Apps List contains a blue box with the number of assets meeting your selection criteria, as shown below.
Filtering Options, Action Icons, and Insights Bar
To the right of the asset count, the Web Apps List offers a dropdown search and filter control and three action icons.
Filtering Options
Clicking on the dropdown search filter allows you to select which Web App assets to display based on the following attributes.
| Action Icons | Function |
|---|---|
|
|
Clicking this icon restricts the dashboard to showing only the Web Apps selected. This is helpful if you know that a Web App is being retired (i.e., taken out of service) in the near future and you do not want the dashboard cluttered by that Web App’s vulnerabilities. |
|
|
Clicking this icon resets the dashboard to its default state.
The reset icon includes an annotation
( |
|
|
Clicking this icon downloads (in CSV format) all details for all or selected Web Apps. |
Filtering Options
The upper right corner of the Web App List contains two filter bars. These allow you to select which Web Apps to display based on the following attributes.
| Filter Type | Definition |
|---|---|
| WEB APP STATUS |
This filter allows you to select Web Apps based on their status. If a Web App is inaccessible and hasn’t been scanned for 30 consecutive days, SP360 will automatically “age-out” (i.e., inactivate/deactivate) that Web App and its associated vulnerabilities. Using this drop-down filter, you can view Web Apps based on the following four options:
Note: Any deactivated Web Apps can be reactivated from the Web App Details page. |
| SCAN RESULT STATUS |
This filter allows you to select Web Apps based on their result of the most recent scan. Available options are:
This filter helps you quickly identify Web Apps that may require follow-up due to scan failures, connectivity issues, or incomplete scan results.
|
| SCAN STATUS |
This filter allows you to view Web Apps based on the current state of their most recent scan. Use this drop-down to focus on scans that have completed, are in progress, or were cancelled. Available options include:
This filter helps you monitor scanning activity in real time or audit recently completed or interrupted scans.
|
| AUTH STATUS |
This filter allows you to view Web Apps based on the authentication outcome from the most recent scan. This is helpful when analysing issues related to login success or credential usage. Available options include:
Use this filter to quickly isolate scans with login issues or verify credential coverage.
|
| FILTER BY DATE |
Web Apps can be filtered based on key lifecycle events and timestamps. Available options include:
These date filters allow you to isolate activity and manage Web Apps based on operational timelines.
|
Action Icons (Bulk Operations)
| Action Icons | Function |
|---|---|
|
|
Clicking this icon restricts the dashboard to showing only the Web Apps selected. This is helpful if you know that a Web App is being retired (i.e., taken out of service) in the near future and you do not want the dashboard cluttered by that Web App’s vulnerabilities. |
|
|
Clicking this icon resets the dashboard to its default state.
The reset icon includes an annotation
( |
|
|
Clicking this icon downloads (in CSV format) all details for all or selected Web Apps. |
Note:
- You can select the checkboxes on the far left to filter the data to display only assets you are interested in. As the boxes are checked, a “Selected” counter appears and is updated, and the graph icon
becomes active. The dashboard will not reflect the changes until the graph icon is clicked.
- Selections are retained across page scrolls, ensuring that any assets you select remain checked as you navigate through the list. To return to the default state, click the
icon.
Web Apps Insights Bar
The Web Apps Insights Bar provides a quick summary of vulnerability severity and scanning activity across all visible web applications. It offers a real-time overview of current risk exposure and operational coverage.
This includes a visual indicator (Severity Bar) followed by several numerical summary tiles, all explained below.
-
SEVERITY Bar: This segmented bar displays the number of vulnerabilities by severity level:
- Urgent – Indicates the highest-risk web application vulnerabilities.
- Critical – Reflects vulnerabilities with significant security consequences.
- Serious – Moderate-level issues requiring attention.
- Medium – Lower-severity findings that may still pose risk.
- Minimal – Informational-level vulnerabilities.
Each segment is color-coded and labelled with the corresponding count of vulnerabilities, enabling users to quickly triage and prioritize based on risk level.
-
Summary Tiles: To the right of the Severity Bar are key numeric indicators that provide contextual scope:
- ACTIVE – Total number of active web applications that will be scanned.
- VULNERABILITIES – Combined count of all detected vulnerabilities across all web apps.
These summary counts update dynamically as filters are applied, providing a real-time overview of the vulnerability landscape tailored to the user's focus area.
The Web App grid includes the following fields by default, however, users can customize the grid to add, remove, or re-arrange fields to meet their needs by clicking the action icon, explained here.
| Column Headers | Definition |
|---|---|
| Name | The assigned name to the Web App. |
| URL | The URL used to navigate to the Web App. |
| VULN COUNT | The total number of vulnerabilities associated with that Web App. |
| Created At | The date on which the Web App was first detected (scanned). |
| Last Scanned | The date on which the Web App was last scanned. |
| Scan Result |
Displays the result of the most recent scan for the given Web App. |
| Actions | Row-level action icons, explained below. |
| Qualys ID | The unique ID assigned to the Web App in Qualys. |
To learn more about the optional fields that can be added, removed, or re-arranged in the Web App grid, click here.
Each Web App has four available icons on the right side of each line.
| Icons | Definition |
|---|---|
|
|
This action icon is used to deactivate scanning of the Web App. |
|
|
This action icon is used to invoke a manual scan of the Web App. A confirmation page is displayed to confirm the request.
To cancel a manual scan, click the revolving “scan in progress”
|
|
|
Clicking this icon displays all vulnerabilities associated with that Web App. For more information about the Vulnerabilities page, click here. |
|
|
Clicking this icon displays detailed information about that Web App, as partially shown below. The Web App details are organized into the following four categories:
|